I create seamless web experiences as a Full Stack Developer. Always excited to catch up 😊
Bangalore, Karnataka - 500036
I create seamless web experiences as a Full Stack Developer. Always excited to catch up 😊
Bangalore, Karnataka - 500036
A deep engineering guide explaining how online card payments work, how PCI compliance protects card data, how tokenization and HSM secure payments, and how tokens are rotated at scale.
Ever wondered how your card details stay safe when you save them on an e-commerce app in India? Let’s take a deep engineering dive into PCI architecture, tokenization, encryption, and the invisible systems protecting every transaction.
If you shop online in India, you’ve seen this checkbox countless times on almost every checkout page:
✅ Save this card for faster checkout
You enter your card details once, tick the box, and next time the app conveniently shows:
💳 **** **** **** 4821
No typing sixteen digits again.
No scrambling for expiry dates.
No friction.
It feels simple. Almost magical.
But behind this tiny checkbox lives one of the most sophisticated security architectures in modern software engineering — designed to protect billions of card transactions every day.
Where exactly is your card stored?
Does any website actually keep your card number?
What happens if servers get hacked?
Why can you only see the last four digits?
Let’s follow the invisible journey of that card.
A card number is not just another string of digits. If leaked, it can instantly enable fraud, chargebacks, regulatory penalties, and reputational damage. History is full of massive breaches caused by poor data isolation and weak encryption.
This is why the global payments ecosystem operates under a strict security standard known as PCI-DSS (Payment Card Industry Data Security Standard). Created by Visa, Mastercard, American Express, Discover, and JCB, PCI applies everywhere in the world — including India.
PCI does not merely say “encrypt your data.”
It defines an entire operating model:
The core philosophy is simple:
👉 Minimize how many systems ever touch real card data.
In India, this also aligns with privacy regulations such as the Digital Personal Data Protection Act (DPDP).
When you type your card details at checkout, it feels like the data flows into the merchant’s backend. In reality, that would be a major security violation.
Modern payment pages embed or redirect card input directly into a PCI-compliant payment gateway. Your browser sends the card details straight into a hardened PCI environment over encrypted channels. The merchant’s application servers never see the raw card number at all.
This separation drastically reduces attack surface. Even if a merchant’s application infrastructure is compromised, attackers cannot retrieve card numbers because they were never there in the first place.
This is the first and most important architectural boundary.
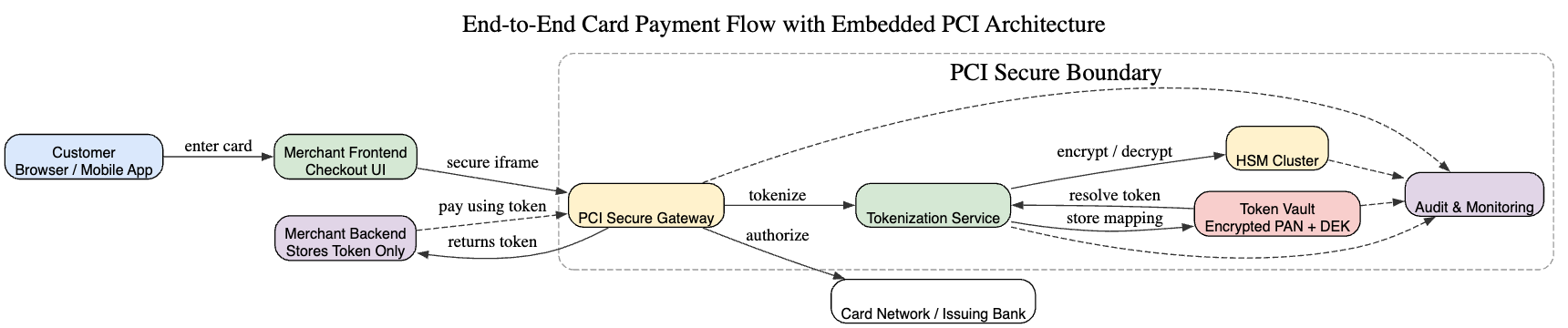
Inside a PCI provider, the system looks very different from a normal cloud application.
The environment is split into multiple isolated zones:
Every layer is tightly controlled. No engineer can casually SSH into these systems. Access is role-based, audited, time-limited, and heavily reviewed.
This architecture deliberately trades convenience for security.
At the heart of the PCI infrastructure sits the Hardware Security Module (HSM).
An HSM is a tamper-resistant hardware device that:
Even administrators cannot extract keys. If someone physically attacks the device, the hardware destroys the secrets instantly.
When card data enters the PCI boundary, it is encrypted almost immediately using keys protected inside the HSM. Plaintext exists only for milliseconds inside controlled memory and is wiped immediately after use.
This creates a hard cryptographic boundary that software alone cannot bypass.
Encrypted card numbers are still inconvenient for large-scale systems. You cannot easily search, correlate, or safely expose encrypted blobs across microservices.
This is where tokenization becomes powerful.
A token is a randomly generated surrogate identifier that represents a card. It has:
Inside the vault, the system stores a mapping:
Token → Encrypted Card Number Only the PCI services can resolve this mapping.
The merchant stores only:
This is why the UI can display masked cards without storing sensitive data.
From a system design perspective, tokenization reduces blast radius dramatically. Even if a merchant database leaks, attackers get meaningless tokens.
Imagine you run a massive warehouse storing millions of lockers. Each locker contains something valuable — in our case, encrypted card data. Now imagine that every time you want to lock or unlock a locker, you must call the central vault manager who holds the master key.
If the warehouse is small, that works. But when you’re processing thousands of payments per second across the globe, that central vault quickly becomes a bottleneck.
This is exactly what would happen if every encryption and decryption operation directly hit an HSM. HSMs are extremely secure, but they are also expensive, slow compared to normal memory operations, and intentionally rate-limited to prevent abuse.
To solve this, large payment systems use a pattern called envelope encryption.
Instead of encrypting card data directly with the master key, the system creates a smaller working key called a Data Encryption Key (DEK). This DEK is used to encrypt and decrypt card data very quickly inside normal application memory. But the DEK itself is encrypted — wrapped — using a master key that lives inside the HSM.
Think of the DEK as a key locked inside a sealed envelope. The envelope is locked using the HSM’s master key. The system can safely store the envelope anywhere, because without the HSM, nobody can open it.
When the system needs to read card data, it sends the encrypted DEK into the HSM. The HSM unwraps it internally and hands back the usable DEK temporarily into protected memory. That DEK decrypts the card data. Once the operation finishes, the DEK is wiped from memory.
This model gives two massive advantages:
Now comes the beautiful part — key rotation at scale.
If a master key ever needs to be rotated for security reasons, the system does not need to re-encrypt billions of card records. Instead, it simply rewraps the DEKs with the new master key. The encrypted card data remains untouched.
Envelope encryption is the invisible backbone that makes large-scale token vaults both fast and secure.
Once a card has been tokenized, the real card number essentially disappears from normal application flow.
The merchant stores only the token — a meaningless identifier that looks like a random string. When a customer returns and pays again, the merchant sends only this token to the PCI provider.
Inside the PCI infrastructure, the tokenization service looks up the token inside the vault. That lookup returns encrypted card data and the encrypted DEK associated with it.
The encrypted DEK is sent into the HSM. Inside the HSM, the master key unwraps the DEK. That usable DEK exists only briefly in protected memory. It decrypts the card data and immediately disappears.
The plaintext card number exists only for a tiny window — just long enough to be transmitted securely to the card network for authorization.
At no point does the merchant see the card number.
At no point does the UI see the card number.
Even most internal services never see the card number.
Sensitive data exists only inside the smallest possible secure bubble.
A common question is: if everything is software, why can’t attackers just hack into the HSM or extract the keys?
The answer is that HSMs are not normal computers. They are purpose-built cryptographic appliances designed to resist both software and physical attacks.
First, HSMs typically do not have general internet access. They sit inside isolated private networks, accessible only by authenticated internal services using mutually authenticated certificates. You cannot simply SSH into them or browse them like a server.
Second, cryptographic keys never leave the hardware in plaintext. Even administrators cannot export them. The hardware enforces this at the silicon level. If someone tries to tamper physically with the device — drilling, opening the casing, probing circuits — the device detects this and automatically wipes the keys.
Third, the firmware running on HSMs is minimal and heavily audited. There is no web server, no package manager, no shell access. The attack surface is intentionally tiny.
Fourth, every cryptographic operation is logged and rate-limited. Abnormal patterns trigger alerts. A compromised application cannot silently abuse the HSM at scale.
Finally, PCI infrastructure uses layered defense. Even if an attacker compromises one service, they still cannot access the vault, cannot access the HSM, cannot unwrap keys, and cannot move laterally because of strict network segmentation and identity controls.
Security here is not about one perfect wall. It is about many independent walls that attackers must break simultaneously — which becomes economically and practically infeasible.
In theory, rotating a cryptographic key sounds scary. If you change a key that encrypts critical data, what happens to all the data already encrypted with the old key? Would payments fail during migration?
At the scale of modern payment systems — millions of cards, billions of encrypted records — brute-force re-encryption would be operationally impossible.
This is why production systems use carefully staged rotation strategies rather than brute replacement.
The master key lives inside the HSM and is responsible only for encrypting (wrapping) data encryption keys, not the card data itself.
When a master key needs to rotate, the system introduces a new master key inside the HSM while keeping the old one temporarily active.
For each DEK stored in the system:
The encrypted card data never changes. Only the wrapped DEKs change.
If anything fails, the old master key remains available and nothing breaks. Once all DEKs are successfully rewrapped and verified, the old master key is securely destroyed.
Payments continue uninterrupted.
DEKs encrypt actual card data. Rotating DEKs requires re-encrypting data, so systems rotate gradually.
New records start using new DEKs immediately. Existing records migrate lazily during low traffic or natural access.
This spreads load safely without spikes.
Tokens remain stable during rotations because they map to encrypted data — not keys.
Customers never notice rotations. Saved cards continue working.
Only real-world card changes trigger token updates.
Large platforms rotate keys region by region.
New master keys exist alongside old ones temporarily. Monitoring ensures safety before global retirement.
If rotation fails, systems safely retry or rollback because old keys remain active.
Security is never compromised.
Rotation happens continuously:
That tiny checkbox hides a massive distributed security platform — cryptography, hardware trust boundaries, isolation layers, monitoring pipelines, and operational rigor.
Your card isn’t sitting casually in a database.
It’s encrypted inside hardware, abstracted behind tokens, protected by layered defenses, and governed by global standards.
Invisible engineering quietly protecting billions of digital transactions every day.
Your email address will not be published. Required fields are marked *